Cybersecurity is Top Business Priority in 2017
How concerned are you about falling prey to cyberattacks in the New Year?
Whether you’re a corporate CEO or a small business owner, strengthening cybersecurity should be a top business priority in 2017. In fact, it should be a “no brainer” by now that every company worldwide needs to get more serious about protecting their information technology (IT) infrastructure to guard against the continuing proliferation of cyber threats.
The U.S. Departmentof Homeland Security (DHS) reminds us:
"Our daily life, economic vitality, and national security depend on a stable, safe, and resilient cyberspace. Yet cyber intrusions and attacks have increased dramatically over the last decade, exposing sensitive personal and business information, disrupting critical operations, and imposing high costs on the economy."
With this in mind, it should be very troubling to anyone online that cyberassaults by rogue hackers continue to skyrocket.
Some global security analysts estimate that hundreds of thousands of attempted cyberattacks occur every minute.
This is a bleak reality of fast evolving technology in the 21st century digital age.
No Failsafe System
In addition to prostituting the privacy of millions of individuals and employees spanning all industries, international cyber criminals can badly damage a company’s brand image and alienate the consumer base, among other detrimental consequences.
That’s why the top business priority in the year ahead should be substantially increasing investments in more potent protection of critical IT infrastructures.
But despite years of incremental progress, it appears there is still no failsafe system to stop sophisticated hackers from causing havoc in cyberspace.
Why are cyber criminals always one step ahead of being caught?
As Wired.com recently reported, “Whether it was a billion compromised Yahoo accounts or state-sponsored Russian hackers muscling in on the US election, this past year [2016] saw hacks of unprecedented scale and temerity. And if history is any guide, next year [2017] should yield more of the same.”
Sony Scathed
I recall the issue of cybersecurity, or lack thereof, capturing mainstream public attention in the USA during late 2014. The harsh realization about our vulnerability in cyberspace occurred in the wake of a severe cyberassault on Sony Pictures in Los Angeles. This resulted in broad international media coverage, as the world renowned movie company initially displayed a knee jerk reaction of denial and damage control.
The Sony cyber breach resulted in embarrassing revelations about business relationships between senior corporate executives and Hollywood movie stars. And the fallout led to the hashtag #Sonygate trending on Twitter for weeks, not to mention some in Sony’s C-suite losing their jobs.
The New York Times reported back then, “Interviews with over two dozen people involved in the episode suggest that Sony — slow to realize the depths of its peril — let its troubles deepen by mounting a public defense only after enormous damage had been done.”
Since then, widespread cyberattacks have become a common casualty of conducting business. The "new normal" of cyber disruptions have caused incalculable productivity losses in the private and public sectors alike. The specific repercussions range from plummeting corporate revenues, to ruined reputations, to dire nationals security risks.
Four Key Threats
According to NetworkWorld.com: “Cyber criminals are becoming more sophisticated and collaborative with every coming year. Looking ahead to 2017, the Information Security Forum (ISF) forecasts businesses will face four key global security threats in 2017.”
The “top four global security threats” identified by the ISF are:
1) “Supercharged connectivity and the IoT will bring unmanaged risks.”
2) “Crime syndicates will take a quantum leap with crime-as-a-service.”
3) “New regulations will bring compliance risks.”
4) “Brand reputation and trust will be a target.”
- Click here for more predictions on cyber threats in 2017.

Interconnected = Vulnerable
In assessing the severity of security flaws in cyberspace, I spoke with several experts in the field.
Charles “Chuck” Brooks is the vice president for government relations and marketing for Sutherland Government Solutions. He served at DHS as the first director of legislative affairs for the Science and Technology Directorate. He ominously points out:
"The reality is that the more digitally interconnected we become in our work and personal lives, the more vulnerable we become." -- Chuck Brooks
Mr. Brooks adds: "Mitigating cyber threats will grow as a priority for business, and for us personally, if we are to commercially function and prosper."
But how can companies successfully mitigate cyber threats?
His advice: "The C-suites and governing boards of corporations will need to invest in better enterprise and endpoint security to prevent phishing and malware probes by hackers. This will also require better training of executives and employees in basic information security measures."
Confronting Cyberterrorism
There’s also the daunting problem of fighting a new wave of so-called "cyberterrorism."
Roque Wicker is the principal of Counter-Terrorism Watch, Inc. The company is a global provider of security consulting and training services based on the West Coast of the USA with offices in Southeast Asia. He says:
“Any New Year's resolution needs to focus on cyber threats." -- Roque Wicker
Mr. Wicker adds: "Without a more robust public/private partnership to combat cyber threats and data breeches, our nation's critical infrastructure and economy could be slowed or even halted -- causing preventable chaos on a scale never seen before."
Looking Ahead
With the U.S. presidential inauguration fast approaching, many in the tech industry are cautiously contemplating how the incoming Trump Administration will improve cybersecurity for government and private industry alike?
Chuck Brooks addresses this crucial question in a recent Federal Times article, writing:
- “One area where DHS is certain to continue to assume a special role and profile is cybersecurity…a major challenge to the nation’s economic and security welfare.”
- “Because of the exponential growth of the Internet of Things, mobile devices, big data and digital commerce, cybersecurity has grown immensely as a key priority while DHS has assumed more of a formal government role in the civilian cyber arena.”
He also points out the following about the President-elect:
- “Trump recently selected Tom Bossert to serve as his White House homeland security adviser. Tom Bossert has a cybersecurity background, and his appointment signals the important role of cybersecurity in the new administration.”
In essence, there's simply no time to waste before the next corporation or government entity falls victim to another crippling cyberattack.
Therefore, swift and bold action to safeguard America's critical IT infrastructure -- and that of all advanced industrialized nations -- is needed now more than ever. No business is safe from increasing cyber threats and no country is immune from the threat of cyber warfare.
Thus, let’s hope the new American president is up to the challenge.
_____________________________________________________________________________________

NOTE: All views and opinions are those of the author only and not official statements or endorsements of any public sector employer, private sector employer, organization or political entity.
Articles from David B. Grinberg
View blog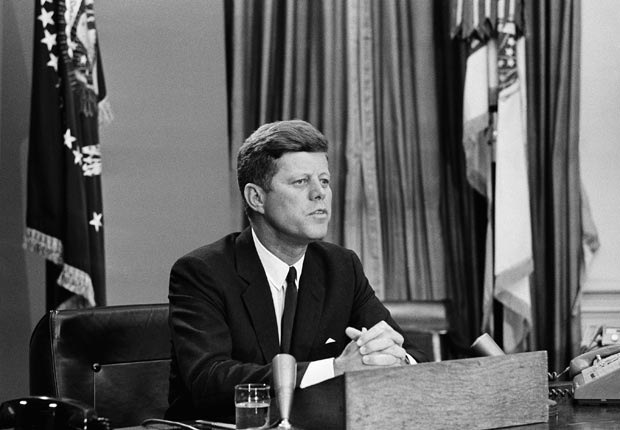
Although President John F. Kennedy was assassinated more than a half-century ago, his strong legacy ...

Happy Birthday America! 🇺🇸💥💥 · Call it coincidence, but did you know that the most sweeping civil ri ...

The date was Nov. 22, 1963. The place was Dallas, Texas. The historic tragedy was the assassination ...
Related professionals
You may be interested in these jobs
-

Budget for recharging the gas of an interior split air conditioning unit"
Found in: Handyman CS US - 2 hours ago
Direct apply
beBee Handyman Shelter Island Heights, NY, United States FreelanceI am in need of an Air Conditioning Installation service in Shelter Island Heights, NY with the following characteristics:Type of work to be done · Gas refill · Type of air conditioning · Indoor split · What technology does the air conditioning have? · Fixed speed · Air condition ...
-
Hair Stylist Intern
Found in: Talent US C2 - 5 days ago
Great Clips Alliance, United States· Are you a cosmetology or barber student who's ready to jump-start your career? Join a locally owned Great Clips salon team and they will help you develop your skills and gain essential salon experience. · Great Clips franchisees aim to assist you: · Familiarize yourself with ...
-
Ingénieur de production H/F
Found in: Talent US 2 C2 - 2 days ago
INETUM Francesville, United StatesMission · Dans le cadre de son développement, la Business Line Infrastructure Services IDF d'Inetum recrute un(e) : Ingénieur de production Linux. Poste basé à Montigny-le-Bretonneux 78 · Vos missions seront les suivantes : · • Suivi de la PROD et résolution des incidents N2 · • ...


Comments
David B. Grinberg
6 years ago #11
David B. Grinberg
7 years ago #10
Thanks so much for your kind words, Donna-Luisa Eversley, in addition to taking the time to read, comment and share. Thanks also for tweeting this post, which is likewise greatly appreciated. Your gracious support and positive social media engagement really means a lot to me. Thanks for being some awesome and BEE-autiful!
David B. Grinberg
7 years ago #9
David B. Grinberg
7 years ago #8
David B. Grinberg
7 years ago #7
David B. Grinberg
7 years ago #6
David B. Grinberg
7 years ago #5
Thanks very much for reading, commenting and sharing this post, Ali Anani. I echo your concerns. My informal understanding is that intelligence communities of various countries are indeed trying to recruit cyber criminals to work for those governments. However, strategic intentions will vary between democracies and authoritarian regimes. Let's hope the good guys can win over the bad guys and make cyberspace a safer place.
David B. Grinberg
7 years ago #4
David B. Grinberg
7 years ago #3
Sarah Elkins
7 years ago #2
David B. Grinberg
7 years ago #1
Thanks so much for your valuable feedback, Joseph Sprute. I appreciate your being the first to comment. cc: Javier \ud83d\udc1d beBee