#cybersecurity
You have no groups that fit your search

Cybersecurity Services
Adina Elsa · Safeguard your #digitalassets and data from #cyberthreats and theft with #Osiz, #cybersecurity service! · · Osiz, a #cybersecuritycompany, provides solutions to all your cyber-related queries and integrates cybersecurity as a defense against #hackers and #maliciousattack. · · ...

Blockchain Cybersecurity Service
Adina Elsa · Time to say goodbye to traditional #security risks and vulnerabilities! Unfold the power of #Blockchain in #cybersecurity with #Osiz! · Protect your #digitalassets, documents, data, and information with our cutting edge Blockchain-based #cybersecurityservice. · Connect with our s ...

Blockchain Development
Adina Elsa · As per #MarketsandMarkets, #blockchain market was around $7.4 billion in 2022 and is expected to grow $94 billion in 2027. · · Worldwide #blockchainsolution has reached $19 billion by 2024 and is estimated to reach $3.1 trillion by 2030. · · Want to participate in the growth ...
Blockchain Cybersecurity
Adina Elsa · Think #cybersecurity - To fight against #cyber attacks! · · Don't leave your #business exposed by tainting your brand and trust. Trust #Osiz to safeguard your #data and information from #cyberthreats. · · Stay ahead of #CyberCriminals! Secure your #digitalfuture and shield th ...

Hire a Professional Hacker to Change Your Academic Grade/Records
Troy Len · Have you been troubled by your poor academic performance. Changing a grade on your college transcript successfully is a difficult undertaking that should not be handled lightly if you want to improve your school grades or earn a university degree. I'll suggest You deal with Smat ...

IT vulnerability assessment
Jessica Smith · Don't let a single vulnerability put your business at risk. Get our guide to IT vulnerability assessment today. · Guide to Conducting An IT Vulnerability Assessment · Today, data is one of your business's most valuable assets. More than that, losing access to your data can stop y ...

SECURITY SOLUTIONS: IT ONLY TAKES ONE VULNERABLE DEVICE
BroadMAX Networks · From phones to fish tanks, you’re only secure as your most vulnerable device. BroadMAX security solutions for devices make it simple to identify, secure and manage every device in your organization from a single, simple-to-use manager. · · · We apply innovative technologies a ...
Health IT
Jaime Contreras, MBA, CISM, CISA · Congress is finally taking medical cybersecurity seriously · There are still huge vulnerabilities in the system. · https://www.theverge.com/2022/6/3/23153048/congress-medical-device-cybersecurity-hacking
Cybersecurity
Jaime Contreras, MBA, CISM, CISA · Council Post: How Failing To Prioritize Cybersecurity Can Hurt Your Company · To strengthen cybersecurity in your company, there are processes that you must implement to achieve it, always considering current threats and the reality in which we live, such as the increase in remot ...

Cyber for Travel
Jaime Contreras, MBA, CISM, CISA · 8 Free or Cheap Cybersecurity Tips for Travelers · Ready to travel? Let’s talk about how you should prepare for vacation and what steps you can take to protect yourself from cyber criminals. · https://clark.com/travel/cybersecurity-tips-for-travelers/
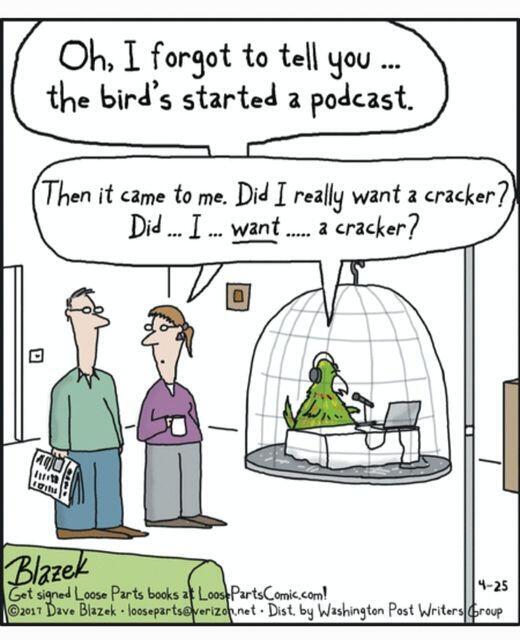
Podcasts these days...
Zacharias 🐝 Voulgaris · Although I may not have the talents of this podcaster, I too have a podcast worth checking out: analyticsandprivacypodcast.buzzsprout.com · #podcasts #analytics #privacy #cybersecurity

Mentoring – Questions and Answers
Zacharias 🐝 Voulgaris · Overview · Mentoring is one of those subjects I can talk about till the cows come home (the other such subjects are the Julia programming language, Data Science, and Cybersecurity). What makes it different, however, is that it's something that appeals to all sorts of professional ...

Health IT - Cybersecurity
Jaime Contreras, MBA, CISM, CISA · OCR director urges providers to strengthen cyber posture, risk management · A new HHS blog post provides a glimpse into the focus of OCR’s HIPAA enforcement for the coming year. Entities are being urged to revamp risk management policies and bolster their cyber posture. · https:/ ...

Podcast to check out!
Zacharias 🐝 Voulgaris · This is something I've been working on for a few months now as I'm passionate about this topic. If you are interested in it, even if you are not a professional in these fields, give it a listen. Cheers! https://analyticsandprivacypodcast.buzzsprout.com · #podcast #analytics #pri ...

Cybersecurity courses for non-experts
Zacharias 🐝 Voulgaris · It's interesting how my 3 Cybersecurity (paid) mini-courses at WintellectNow are still highly relevant even a year after their publication. Designed with non-experts in mind, these courses can help you get your bearings in hands-on matters of Cybersecurity, from managing private ...

Cyber Defense
Jaime Contreras, MBA, CISM, CISA · Cybersecurity: 11 steps to take as threat levels increase | ZDNet · Security agency warns businesses that the cyber-threat level rises when zero days or geopolitical tensions emerge. · https://www.zdnet.com/article/cybersecurity-11-steps-to-take-as-threat-levels-increase/

Cyversity Membership
Jaime Contreras, MBA, CISM, CISA · Become a Member · Building Diversity & Inclusion into the Fabric of Cybersecurity · The stakes within cybersecurity have never been greater. The need for diversity among the professionals entrusted with guarding our technology infrastructure has never been more evident or critic ...

Vlad Nov - Guide to Cybersecurity Planning For Business
Vlad Nov · #Cybersecurity programs incorporate a variety of processes and tools designed to help organizations deter, detect, and #blockthreats. Contact VladNov for more info! ·

Facebook's Recent Issues and the Need for More Privacy
Zacharias 🐝 Voulgaris · Source: pixabay.com · Brief Overview of What's Happened · It’s no secret that Facebook has been on a losing streak lately. Not something you would expect from a prestigious tech company that’s become a household name for years now. Then again, we live in bizarre times where lots ...

Cyber Security Lead Generation: Where and How To Look for New Leads in 2021
Judy Caroll · Cyber security lead generation is a niche B2B market with its own rules meaning not every single marketing tactic in the hat is going to work for the market. · However, by understanding the target customers, there are plenty of opportunities for marketers to leverage the uniqu ...
Related professionals
You may be interested in these jobs
-
Nurse Manager
3 days ago
Insero Talent Solutions Rochester, United StatesJob Description · Job Description · Insero Talent Solutions is recruiting a Nurse Manager for an exclusive senior living community in Rochester, NY. · Position Summary: · The nurse manager is responsible for the supervision and management of the nursing department, the organiza ...
-

Client Service Representative
2 days ago
Burlington Emergency & Veterinary Specialists Williston, United StatesJob Description · Job DescriptionJoining a clinic with its own unique identity is like a cross-country car ride with your ears flapping in the breeze. Burlington Emergency & Veterinary Specialists is looking to add compassionate and skilled Client Service Representatives to our t ...
-
pittston cdl-a delivery driver
17 hours ago
US Foods Holding Corp Port Griffith, PA , USA, United StatesSafely drive trucks to customers and meet scheduled customer delivery times. Carefully unload products from the trailer with a two-wheeler, pallet jack, or by hand and place in designated customer storage areas. Verify accuracy of delivery with custo Delivery Driver, CDL, Deliver ...
-
#leadership 76 posts
-
#ai 55 posts
-
#power 43 posts
-
#austinrotter 43 posts
-
#gemsny 42 posts
-
#usa 42 posts
-
#article 40 posts
-
#brooklynnchandlerwilly 39 posts
-
#todaymatters 36 posts
-
#mg 36 posts
Get the most out of your content


